spring security动态配置url权限认证
本文介绍的spring security动态配置url权限认证基于的是spring-boot-2.0.0、spring-security 5.X来编写的。笔者浏览完spring security官方文档之后,发现并没有详细的介绍说明如何动态的配置我们的url权限认证。spring security默认的权限配置确只会在启动工程的时候初始化一次url权限配置。但是实际情况我们项目的权限会随时动态的更
本文介绍的spring security动态配置url权限认证基于的是spring-boot-2.0.0、spring-security 5.X来编写的。
笔者浏览完spring security官方文档之后,发现并没有详细的介绍说明如何动态的配置我们的url权限认证。spring security默认的权限配置确只会在启动工程的时候初始化一次url权限配置。但是实际情况我们项目的权限会随时动态的更改,这样我们就需要重新启动项目以便新配置的权限生效。这样的处理显然不合理。当然spring是具有非常好的拓展性,我们就抓主spring的这个特性,模仿默认的认证方式来拓展我们需要的认证规则。
在spring security的官方文档的Spring Security FAQ里有这么一个问题解答44.4.6. How do I define the secured URLs within an application dynamically?
这里的解答非常重要
1.需要提供认证数据规则源数据(类似默认配置在代码里的url权限数据)
2.自定义一个拦截器然后把它添加到spring security的filterChain中
通过这两个主要思路,在逐步通过来代码来实现我们的动态url权限配置
具体步骤
1.配置认证数据源
public class MyFilterSecurityMetadataSource implements FilterInvocationSecurityMetadataSource {
private final Map<RequestMatcher, Collection<ConfigAttribute>> requestMap;
/*
* 这个例子放在构造方法里初始化url权限数据,我们只要保证在 getAttributes()之前初始好数据就可以了
*/
public MyFilterSecurityMetadataSource() {
Map<RequestMatcher, Collection<ConfigAttribute>> map = new HashMap<>();
AntPathRequestMatcher matcher = new AntPathRequestMatcher("/home");
SecurityConfig config = new SecurityConfig("ROLE_ADMIN");
ArrayList<ConfigAttribute> configs = new ArrayList<>();
configs.add(config);
map.put(matcher,configs);
AntPathRequestMatcher matcher2 = new AntPathRequestMatcher("/");
SecurityConfig config2 = new SecurityConfig("ROLE_ADMIN");
ArrayList<ConfigAttribute> configs2 = new ArrayList<>();
configs2.add(config2);
map.put(matcher2,configs2);
this.requestMap = map;
}
/**
* 在我们初始化的权限数据中找到对应当前url的权限数据
*
* @param object
* @return
* @throws IllegalArgumentException
*/
@Override
public Collection<ConfigAttribute> getAttributes(Object object) throws IllegalArgumentException {
FilterInvocation fi = (FilterInvocation) object;
HttpServletRequest request = fi.getRequest();
String url = fi.getRequestUrl();
String httpMethod = fi.getRequest().getMethod();
// Lookup your database (or other source) using this information and populate the
// list of attributes (这里初始话你的权限数据)
//List<ConfigAttribute> attributes = new ArrayList<ConfigAttribute>();
//遍历我们初始化的权限数据,找到对应的url对应的权限
for (Map.Entry<RequestMatcher, Collection<ConfigAttribute>> entry : requestMap
.entrySet()) {
if (entry.getKey().matches(request)) {
return entry.getValue();
}
}
return null;
}
@Override
public Collection<ConfigAttribute> getAllConfigAttributes() {
return null;
}
@Override
public boolean supports(Class<?> clazz) {
return FilterInvocation.class.isAssignableFrom(clazz);
}
这里使用不了WebExpressionConfigAttribute这个类配置ConfigAttribute,应为它只能在package中使用,这也导致了在认证管理器中,我们不能使用对应WebExpressionVoter来解析我们使用的SecurityConfig加载的数据。具体原因如下
:
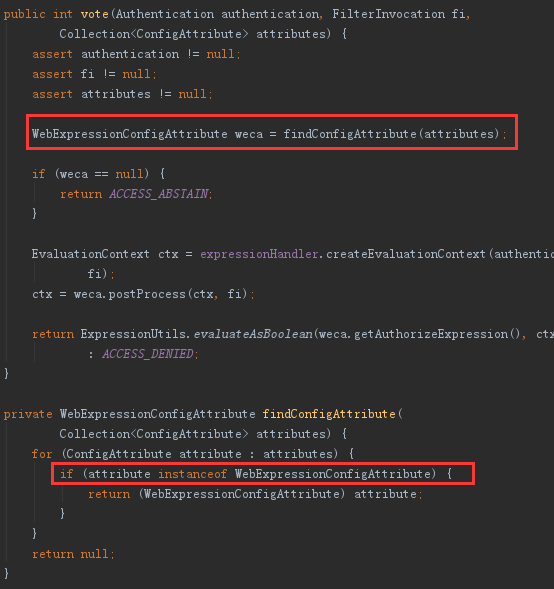
这里做了一个类的实例检查。所以在后面使用了RoleVoter来做认证数据的解析。
2.自定义动态数据拦截器
public class DynamicallyUrlInterceptor extends AbstractSecurityInterceptor implements Filter {
//标记自定义的url拦截器已经加载
private static final String FILTER_APPLIED = "__spring_security_filterSecurityInterceptor_filterApplied_dynamically";
private FilterInvocationSecurityMetadataSource securityMetadataSource;
private boolean observeOncePerRequest = true;
@Override
public Class<?> getSecureObjectClass() {
return FilterInvocation.class;
}
@Override
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain) throws IOException, ServletException {
FilterInvocation fi = new FilterInvocation(request, response, chain);
invoke(fi);
}
@Override
public void init(FilterConfig filterConfig) throws ServletException {
}
@Override
public void destroy() {
}
public FilterInvocationSecurityMetadataSource getSecurityMetadataSource() {
return this.securityMetadataSource;
}
public SecurityMetadataSource obtainSecurityMetadataSource() {
return this.securityMetadataSource;
}
public void setSecurityMetadataSource(FilterInvocationSecurityMetadataSource newSource) {
this.securityMetadataSource = newSource;
}
@Override
public void setAccessDecisionManager(AccessDecisionManager accessDecisionManager) {
super.setAccessDecisionManager(accessDecisionManager);
}
public void invoke(FilterInvocation fi) throws IOException, ServletException {
if ((fi.getRequest() != null)
&& (fi.getRequest().getAttribute(FILTER_APPLIED) != null)
&& observeOncePerRequest) {
// filter already applied to this request and user wants us to observe
// once-per-request handling, so don't re-do security checking
fi.getChain().doFilter(fi.getRequest(), fi.getResponse());
}
else {
// first time this request being called, so perform security checking
if (fi.getRequest() != null) {
fi.getRequest().setAttribute(FILTER_APPLIED, Boolean.TRUE);
}
InterceptorStatusToken token = super.beforeInvocation(fi);
try {
fi.getChain().doFilter(fi.getRequest(), fi.getResponse());
}
finally {
super.finallyInvocation(token);
}
super.afterInvocation(token, null);
}
}
这个类参考的是FilterSecurityInterceptor这个类写的,只是修改了FILTER_APPLIED的值。主要是重写了父类的方法,添加认证数据源值的设置。使父类在调用方法是能找到对应的数据。
3.提供一个认证管理器
public class DynamicallyUrlAccessDecisionManager extends AbstractAccessDecisionManager {
public DynamicallyUrlAccessDecisionManager(List<AccessDecisionVoter<?>> decisionVoters) {
super(decisionVoters);
}
@Override
public void decide(Authentication authentication, Object object, Collection<ConfigAttribute> configAttributes)
throws AccessDeniedException, InsufficientAuthenticationException {
int deny = 0;
for (AccessDecisionVoter voter : getDecisionVoters()) {
int result = voter.vote(authentication, object, configAttributes);
if (logger.isDebugEnabled()) {
logger.debug("Voter: " + voter + ", returned: " + result);
}
switch (result) {
case AccessDecisionVoter.ACCESS_GRANTED:
return;
case AccessDecisionVoter.ACCESS_DENIED:
deny++;
break;
default:
break;
}
}
if (deny > 0) {
throw new AccessDeniedException(messages.getMessage(
"AbstractAccessDecisionManager.accessDenied", "Access is denied"));
}
// To get this far, every AccessDecisionVoter abstained
checkAllowIfAllAbstainDecisions();
}
}
spring security默认提供了
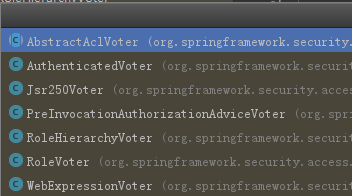
有这么几种具体的认证决策,这里最终使用的是RoleVoter这个决策认证类。
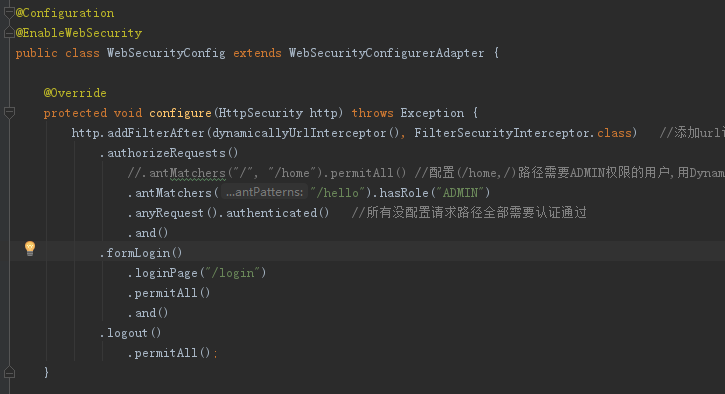
4.配置filter
@Bean
public DynamicallyUrlInterceptor dynamicallyUrlInterceptor(){
DynamicallyUrlInterceptor interceptor = new DynamicallyUrlInterceptor();
interceptor.setSecurityMetadataSource(new MyFilterSecurityMetadataSource());
//配置RoleVoter决策
List<AccessDecisionVoter<? extends Object>> decisionVoters = new ArrayList<AccessDecisionVoter<? extends Object>>();
decisionVoters.add(new RoleVoter());
//设置认证决策管理器
interceptor.setAccessDecisionManager(new DynamicallyUrlAccessDecisionManager(decisionVoters));
return interceptor;
}
然后在把我们的filter添加到spring security的filter中
附上spring security的fiter信息的连接
https://docs.spring.io/spring-security/site/docs/4.2.4.RELEASE/reference/htmlsingle/#ns-custom-filters
最后,本例子只是技术探讨。具体使用这种动态的url验证机制是否合适,还需要结合实际情况来分析。
项目地址:https://gitee.com/longguiyunjosh/spring-security-dynamically-demo
参考文章:
https://segmentfault.com/a/1190000010672041
https://www.cnblogs.com/visoncheng/p/3335768.html
作者:说你还是说我
链接:https://www.jianshu.com/p/0a06496e75ea
来源:简书
更多推荐
 已为社区贡献4条内容
已为社区贡献4条内容









所有评论(0)