ElasticSearch 7配置密码认证及创建用户
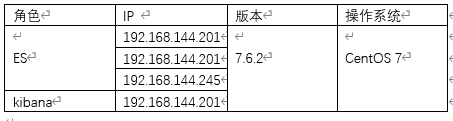
一 背景介绍我们直接安装的ES默认是没有账号与密码的,输入ES服务器的ip:端口,直接就能返回结果,非常不安全:因此需要设置账号密码。我这里的实验环境:二 创建用户2.1 在ES节点上设置用户密码2.1.1 在其中一个节点上生成认证文件必须要生成认证文件,且ES配置文件里要引用这些生成的认证文件,否则启动ES的时候,日志会报错:Caused by: javax.net.ssl.SSLHandsha
一 背景介绍
我们直接安装的ES默认是没有账号与密码的,输入ES服务器的ip:端口,直接就能返回结果,非常不安全:

因此需要设置账号密码。
我这里的实验环境:
二 创建用户
2.1 在ES节点上设置用户密码
2.1.1 在其中一个节点上生成认证文件
必须要生成认证文件,且ES配置文件里要引用这些生成的认证文件,否则启动ES的时候,日志会报错:Caused by: javax.net.ssl.SSLHandshakeException: No available authentication scheme。
虽然ES看起来启动成功了,但是集群状态是异常的。
2.1.1.1 生成CA证书
[EsUser@localhost ~]$ elasticsearch-certutil ca
……
Please enter the desired output file [elastic-stack-ca.p12]: #这里直接回车即可
Enter password for elastic-stack-ca.p12 : #这里直接回车即可,不要设置密码
设置完毕后,会在/usr/local/elasticsearch-7.6.2下看到新生成的文件:
elastic-stack-ca.p12
/*
假如在生成证书的时候设置了密码,会导致无法启动ES,报错:
ElasticsearchSecurityException[failed to load SSL configuration [xpack.security.transport.ssl]]; nested: ElasticsearchException[failed to create trust manager]; nested: ElasticsearchException[failed to initialize SSL TrustManager]; nested: IOException[keystore password was incorrect]; nested: UnrecoverableKeyException[failed to decrypt safe contents entry: javax.crypto.BadPaddingException: Given final block not properly padded. Such issues can arise if a bad key is used during decryption.];
Likely root cause: java.security.UnrecoverableKeyException: failed to decrypt safe contents entry: javax.crypto.BadPaddingException: Given final block not properly padded. Such issues can arise if a bad key is used during decryption.
*/
2.1.1.2 生成p12秘钥
#使用第一步生成的证书,生成p12秘钥
elasticsearch-certutil cert --ca elastic-stack-ca.p12
下面三项直接回车即可:
……
Enter password for CA (elastic-stack-ca.p12) :
Please enter the desired output file [elastic-certificates.p12]:
Enter password for elastic-certificates.p12 : #这里直接回车即可,不要设置密码,否则后面ES会启动不了
Certificates written to /usr/local/elasticsearch-7.6.2/elastic-certificates.p12
设置完毕后,会在/usr/local/elasticsearch-7.6.2下看到新生成的文件:
elastic-certificates.p12
#拷贝p12秘钥文件
cd /usr/local/ElasticSearch/config
mkdir certs
cp /usr/local/elasticsearch-7.6.2/elastic-certificates.p12 certs/
2.1.2 将p12认证文件拷贝到其他节点上
在其他节点上先创建下certs目录:
cd /usr/local/ElasticSearch/config
mkdir certs
拷贝文件:
scp /usr/local/ElasticSearch/config/certs/elastic-certificates.p12 192.168.144.202:/usr/local/ElasticSearch/config/certs/elastic-certificates.p12
scp /usr/local/ElasticSearch/config/certs/elastic-certificates.p12 192.168.144.245:/usr/local/ElasticSearch/config/certs/elastic-certificates.p12
2.1.3 修改所有ES节点的配置文件
vi /usr/local/ElasticSearch/config/elasticsearch.yml
添加:
xpack.security.enabled: true
xpack.security.transport.ssl.enabled: true
xpack.security.transport.ssl.verification_mode: certificate
xpack.security.transport.ssl.keystore.path: certs/elastic-certificates.p12
xpack.security.transport.ssl.truststore.path: certs/elastic-certificates.p122.1.4 重启各ES节点
关闭命令略。
启动命令:elasticsearch -d
2.1.5 设置密码
#前提条件
想要成功设置密码的话,必须确保集群状态正常才行,否则密码设置会失败。
在其中一个节点上设置密码即可:
/usr/local/ElasticSearch/bin/elasticsearch-setup-passwords interactive
Initiating the setup of passwords for reserved users elastic,apm_system,kibana,logstash_system,beats_system,remote_monitoring_user.
You will be prompted to enter passwords as the process progresses.
Please confirm that you would like to continue [y/N]y
Enter password for [elastic]:
Reenter password for [elastic]:
Enter password for [apm_system]:
Reenter password for [apm_system]:
Enter password for [kibana]:
Reenter password for [kibana]:
Enter password for [logstash_system]:
Reenter password for [logstash_system]:
Enter password for [beats_system]:
Reenter password for [beats_system]:
Enter password for [remote_monitoring_user]:
Reenter password for [remote_monitoring_user]:
Changed password for user [apm_system]
Changed password for user [kibana]
Changed password for user [logstash_system]
Changed password for user [beats_system]
Changed password for user [remote_monitoring_user]
Changed password for user [elastic]2.1.6 登录验证
这里用elastic账号登录:


--相对于之前的可以无密码直接访问,现在需要输入密码才能访问ES了。
2.2 配置kibana用户密码
由于ES设置了密码,kibana也无法无密码访问了,也需要对kibana进行相应设置。
2.2.1 修改配置文件
vi /usr/local/kibana/config/kibana.yml
添加:
elasticsearch.username: "kibana"
elasticsearch.password: "密码"
这里的密码处填写‘2.1.5’里为kibana用户设置的密码。
2.2.2 重启kibana
#启动
/usr/local/kibana/bin/kibana &
2.2.3 登录验证

登录成功,但是,信息无法查看。权限没开通,返回如下信息。
{"statusCode":403,"error":"Forbidden","message":"Forbidden"}
用超级用户elastic用户可成功登录。
点击左下角的管理按钮->Security->Users,可以看到我们之前配置过密码的用户:

这些默认用户的角色无法修改,可自己新建角色和用户,来满足自己的使用需求。
2.3 在kibana里创建程序账号
想建一个有增删改查权限的程序账号,提供给程序使用。
2.3.1 创建角色

#给该角色授予操作所有索引的读写权限及创建索引的权限
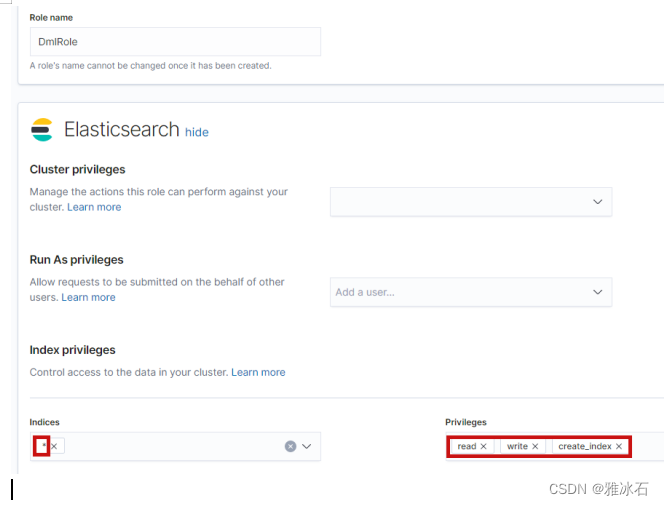
点击下面的'create role'创建角色。
2.3.2 创建用户


需要赋予该用户kibana_admin权限,否则新用户没权限登录,报错:
{"statusCode":403,"error":"Forbidden","message":"Forbidden"}
#也可以直接用命令创建角色及账号。
#创建角色
curl --user elastic:密码 -H "Content-Type: application/json" -XPUT http://172.18.252.101:10412/_security/role/DmlRole -d '{
"indices": [
{
"names": [
"*"
],
"privileges": [
"read",
"write",
"create_index"
]
}
]
}'注释:
names:指定索引
privileges:权限类别
#创建账号
curl --user elastic:密码 -H "Content-Type: application/json" -XPOST http://172.18.252.101:10412/_security/user/ProgramUser -d '{
"password" : "密码",
"roles" : ["DmlRole","kibana_admin"]
}'
更多推荐
 已为社区贡献24条内容
已为社区贡献24条内容







所有评论(0)